Businesses have a lot to consider when managing outside threats — especially in the world of rapidly-growing data breaches. Among the top of the list is one problem that should get business owners’ attention: credit card skimmers.
Credit card skimmers are essentially highly-sophisticated devices placed inside or over top of ATMs and point-of-sale terminals to steal, or “skim,” credit card credentials. Both fraudsters’ techniques and the technology used to skim the credit card details have become incredibly advanced.
The evolution of credit card skimmers has created serious security threats that every organization must be prepared to combat. We’ve laid out how you can quickly identify if your business is at risk and how to avoid this growing problem.
Spotting Credit Card Skimmers: The Physical Inspection
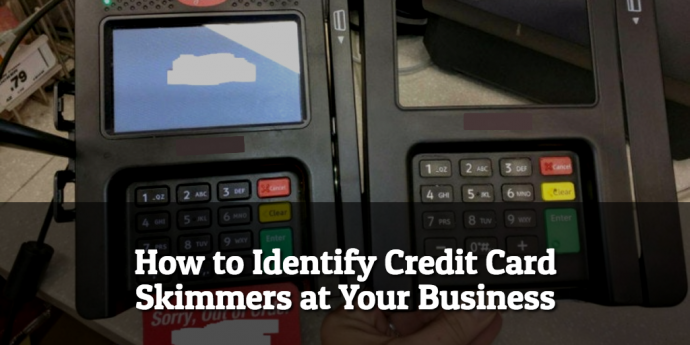
The first step to identifying a credit card skimmer is to inspect your terminal and PIN pads regularly. Although the differences will be minor, a modified terminal will often have defects or different types of materials where the skimmer was inserted. You should look to see if any pieces are loose, or if there are any minor alterations to the design of the terminal itself.
Another major way credit card data is stolen is through pinhole cameras near PIN pads that allow hackers to steal credit card numbers via cameras. The PIN pad itself is a major entry point for skimmers. Ensure your PIN pad doesn’t have an overlay installed that could lead to PIN theft. Although subtle, you should be able to spot if a PIN pad was modified. This is the first step to securing your business and customers from outside skimming threats.
Checking for tampering at payment terminals should be a business practice that’s as common as locking the doors at the end of the evening. Just as you need to protect your physical business, you need to invest in measures that prevent your payment terminals from being compromised.
Regularly checking for tampering, inspecting PIN pads, and checking the device material are all sure ways to protect your business from falling victim to credit card skimming schemes. If your business has an ATM inside of it, you should be relying on the same steps to inspect your ATMs as that’s another popular way fraudsters skim payment data.
Detecting Credit Card Skimmers: Better Security Software
Credit card skimmers can be as thin as a credit card itself and often are inserted into a machine without any physical change to the outside. This makes detection harder unless the inside of the device is physically inspected. Since that’s not always possible, make sure that you use terminal fraud security software so you are alerted the moment a skimmer device is installed.
Even with the implementation of EMV, ATM skimming is still a major threat to any businesses accepting credit cards. In fact, there’s an even newer trend on the market referred to as EMV “shimming,” which involves putting a “shim” between the chip and the card that allows the chip data to be stolen when the card is inserted into the device. More than ever, this is why businesses must invest in detection devices and better security software.
Even as merchants shift toward EMV to protect themselves, techniques such as shimming will be used to steal credit card numbers through more inconspicuous manners. EMV shimming, and similar techniques, are projected to continue to be used by fraudsters — even as businesses invest in better security measures by upgrading their payment terminals to be EMV-compliant. The only way businesses can keep up with hackers is by investing in technology that detects skimmers and shimmers as they compromise payment terminals and credit/debit cards.
Why Credit Card Skimming Is Still a Major Threat
Skimmers used to be clunky machines that were easy to spot simply by looking at a payment device. Fraudsters, of course, have upped their skimming game and created devices that are slimmer and designed to be inserted deeper into devices. This has made skimmers more effective and harder to detect. And that’s just the tip of the iceberg.
Fraudsters also no longer need to work with the physical skimmer to steal the payment credentials. Now, cell phone SIM cards and Bluetooth technology have made it possible for hackers to steal massive amounts of payment data in a shorter amount of time. They’re also accelerating the rate at which that data is compromised by selling credit card numbers online, making an even bigger mess for businesses who take payments from stolen credit cards,
Even though the business didn’t cause the hack, having a device that leads to a customer’s card number being stolen can create a negative brand experience and cause compliance problems with your card issuing partners. In today’s competitive ecosystem, businesses cannot afford to be associated with data breaches, chargebacks or stolen credit cards. Investing in better software security and newer payment hardware are two sure ways to protect yourself and your customers. If you have any questions about protecting your business, don’t hesitate to reach out! Our security specialists can help to ensure your business and customers are fully protected. Give us a call at (888) 638-7867 or visit us online at www.goemerchant.com/contact-us